Preparing for the End of Default Outbound Access in Azure
VDI professional with 6+ years of hands-on experience across Citrix, Windows 365, and Azure Virtual Desktop. Passionate about exploring emerging technologies, I share practical, real-world insights, step-by-step guides, and troubleshooting tips on Modern Workplace technologies.
Microsoft has announced that after March 31, 2026, any newly created Virtual Network will not have implicit Default Outbound Access enabled. Microsoft now recommends managing outbound traffic explicitly.
What is Default Outbound Access?
Default Outbound Access is essentially a fallback mechanism. If a subnet did not have any explicit outbound configuration such as:
Instance level Public IP
NAT Gateway
NVA/Firewall
Load Balancer outbound rules
Azure would automatically perform Source Network Address Translation using a Microsoft managed public IP address to allow outbound internet connectivity.
This public IP was platform managed, not visible as a resource in the Azure Portal, and not directly associated with the virtual machine or its network interface.
What Is Changing?
With the upcoming API update, the defaultOutboundAccess property for subnets will be set to false by default.
This means:
Newly created subnets will automatically be private
No default public IP will be assigned
Outbound access must be configured intentionally
The changes aims for:
Improve overall network security posture
Reduce unintended internet exposure
Align with zero trust principles
Prevent disruption caused by non customer owned IP changes
Impact on Existing Virtual Networks
There is no immediate impact on existing Virtual Networks or subnets.
They will continue to function as they do today.
The update only applies to newly created Virtual Networks and subnets after March 31, 2026.
That said, it is advisable for organizations to start planning explicit outbound management even for existing environments.
Applicability to Windows 365
In Windows 365, networking depends on how the environment is configured.
Microsoft Hosted Network
In this model, Cloud PCs are provisioned in a Microsoft managed network.
Customers do not manage the backend Virtual Network. There is no impact from this announcement and no action is required.
Azure Network Connection
If Windows 365 is configured using Azure Network Connection, the behavior depends on the subnet.
Existing subnets will continue to work without issue.
However, for any new subnet created in the future, outbound connectivity must be configured explicitly.
If internet routing is not defined properly:
Azure Network Connection validation checks will fail
Cloud PC provisioning will fail
Some services such as Windows Activation require direct internet connectivity, so proper outbound routing becomes critical.
Impact on Azure Virtual Desktop
For existing Azure Virtual Desktop environments, there is no immediate impact. Customers can continue adding virtual machines to existing host pools.
However, when creating new Virtual Networks or new subnets for expansion, outbound traffic must be explicitly managed.
Even though existing networks are unaffected, it is a good practice to proactively disable Default Outbound Access and implement controlled outbound architecture.
How to Disable Default Outbound Access
Default Outbound Access is configured at the subnet level.
To disable it for an existing subnet:
Navigate to the Virtual Network
Select the desired subnet
Click the checkbox to Enable the Private Subnet.

Save the configuration
Default Outbound Access should be disabled only when a controlled and explicitly designed egress path is already in place to avoid unintended loss of internet connectivity.
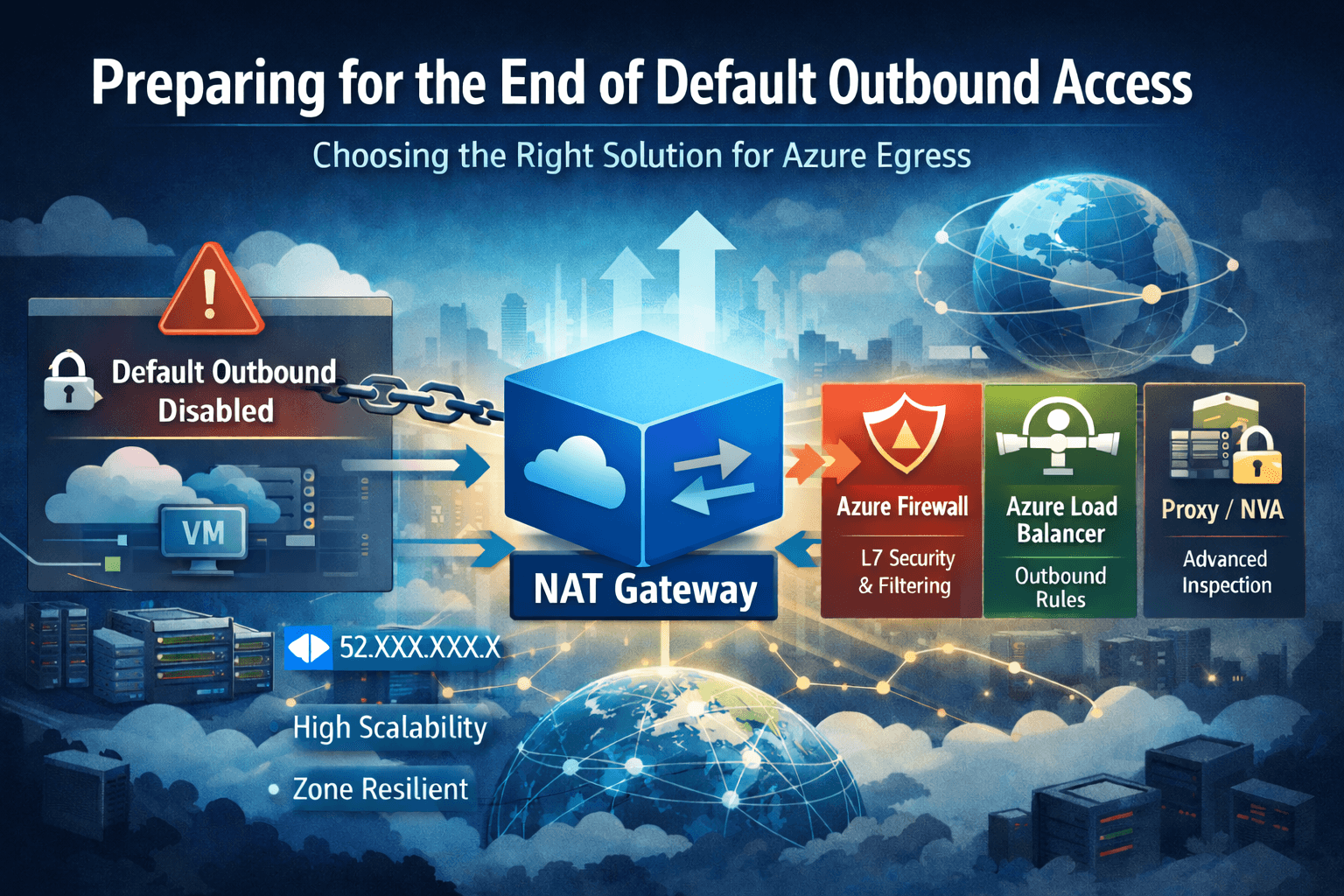
Managing Outbound Traffic Explicitly
Azure NAT Gateway
Azure NAT Gateway is Microsoft’s recommended solution for most outbound connectivity scenarios.
It enables secure and scalable outbound internet access while keeping virtual machines private and unreachable from inbound internet traffic.
Benefits
Predictable static Public IP or Public IP Prefix
No inbound exposure
Fully managed and highly available
Simple subnet level association
How It Works

In the depicted Topology:
DOA-VNET represents the Virtual Network
default represents the private subnet
NATgateway represents the NAT Gateway
PIP represents the Public IP Prefix
When VM sends a request to the internet, the subnet routes the traffic to the associated NAT Gateway.
The NAT Gateway translates the private IP address of the VM into a public IP address from the Public IP Prefix and sends the request to the destination.
When the response returns, the NAT Gateway validates the session using its state table and maps the response back to the original private IP address of the VM.
The VM remains private throughout the process while still having secure outbound connectivity.
Azure Firewall
Azure Firewall is a cloud native security service deployed inside a Virtual Network.
It sits between your Azure environment and the internet or on premises network to centrally inspect and control traffic.
It is suitable when you require:
Layer 3 to Layer 7 filtering
FQDN based rules
Threat intelligence protection
TLS inspection in Premium SKU
Intrusion Detection and Prevention
Azure Firewall is available in Basic, Standard, and Premium SKUs.
Considerations
Higher cost compared to NAT Gateway
Possible additional latency due to inspection
Requires proper routing configuration
Other Outbound Connectivity Options
Azure Load Balancer can provide outbound connectivity using outbound rules. In some cases, instance level Public IP addresses may also be used for direct outbound access.
However, each option should be evaluated carefully based on security, scalability, and operational requirements.
Conclusion
The upcoming change to Default Outbound Access reflects Microsoft’s continued focus on strengthening secure and intentional network design in Azure.
For many organizations, this update may have little to no impact, as explicit outbound connectivity using NAT Gateway, Azure Firewall, or other controlled methods is already a common best practice.
However, it remains a good opportunity to review existing environments, confirm there is no reliance on implicit outbound access, and ensure outbound traffic is aligned with security and governance standards.
Overall, this update reinforces structured network architecture without introducing disruption for well designed environments.